A friend asked me a question today. Is the Cloud safe? She feels like a Luddite because she’s not using it, but she really doesn’t feel like it’s safe. I’ve talked to a number of people who feel the same way. Some people think that their data in the Cloud will be stolen in some fashion. Others tell they’re afraid that their data will be taken out of context and they’ll be hauled off to jail. So, what’s the answer?
 Is the Cloud safe?
Is the Cloud safe?
Well, yes it is.
The Cloud is the safest place I’ve found to store my data. This is because my data backup is on automatic pilot. When I change a file and save it, it gets updated to my computer AND to Dropbox. We’ve had several customers who use an external hard drive to back up there data once a week or once a month. The trouble there is that people are fallible. People don’t always remember to do a task. They may have set up a calendar alarm to remind them to back up their data, but decide when it goes off that they will do it “later”. And “later” never comes. Those customers I mentioned earlier then had their hard drive crash, but hadn’t backed up their data in six months or a year.
So, is the Cloud Safe?
Well, no, it’s really not.
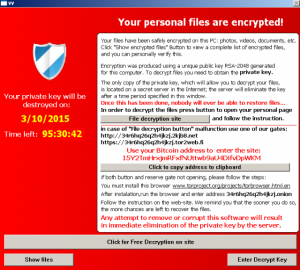
There have been several instances where the “bad guys” have broken into databases and stolen data. One instance last year when a Password Manager was hacked and thousands of passwords were compromised. (Which is why I am constantly harping on folks to change their passwords frequently!)
Another concern according to MalwareBytes that many people (and companies) have is: “It’s physically out of your hands. You aren’t saving to a hard drive at your house. You are sending your data to another company, which could be saving your data thousands of miles away, so keeping that information safe is now dependent on them.”
It’s really your call. Convenience vs. keeping your data physically in your possession. But, if you have precious data that changes frequently, I really recommend the Cloud. Oh, and change your password!
Chris Eddy of Geek For Hire, Inc. has been providing computer service to families and small businesses with Mac’s and PC’s for the past fifteen years. His company is highly rated by both the BBB (Better Business Bureau) and by Angie’s List. You can find more on our website, or give us a call 303-618-0154. Geek For Hire, Inc. provides onsite service (Tier 3) to the Denver / Boulder / Front Range area as well as remote service throughout North America.
We’ve been using Amazon Prime for the past few years. We like the free 2-3 day shipping and the online streaming. I haven’t tried the Kindle lending library yet. I’ll try that next! Prime is normally $99/year, but you can try it for 30 day for free by clicking on this link: Try Amazon Prime 30-Day Free Trial (Yes, we’ll get a small commission if you sign up.)