The Router Virus
Have you heard in the past few weeks about the router virus that is impacting hundreds of thousands of routers? The FBI even issued a report recommending that everyone reboot their routers because:
“Foreign cyber actors have compromised hundreds of thousands of home and office routers and other networked devices worldwide.”
Over the past week or so, we’ve been getting calls from our customers who are very concerned about the router virus they keep hearing about. And they’re right to be concerned. The malware has been programmed into hundreds of thousands of routers. Big deal, right? Because I don’t run any programs on my router, I’m protected, right? I don’t store any of my data on my router. It’s just that black box that sits in the corner that brings my WiFi signal from my ISP to my tablet. Completely harmless, right?
What can go wrong?
Harmless? Well, no. This particular router virus can make your router inoperable. Even worse, it can collect any information passing through the router. And then it could possibly collect your ID and password for your bank account.
How do you protect yourself?
The FBI is recommending that you reboot your device and then upgrade to the latest firmware. You should also change the router password to a super-super secure password.
How do you reboot your router?
Rebooting your router is just like rebooting your computer. Unplug the router (or turn it off if the on/off switch is clearly marked), Wait 30 seconds, then plug it back in.
Will a reboot of the router always work?
Several privacy and security companies are saying that a reboot does a partial job. Apparently, a router has two kinds of memory: Volatile and non-volatile memory. Sometimes the router virus will also write data to the non-volatile memory too. A reboot will clear volatile memory only. In order to clear non-volatile memory, you’ll need to reset your router.
Should I reset my Router instead?
A router reset is more complicated than just turning the device off and on. You’ll need to enter certain information and then follow certain steps. ESET (the company we like for antivirus software) has provided instructions for performing the reset. You can find them in this article.
Which routers have this virus?
ESET has published a list of routers known to be infected with the router virus. There are probably many others and the best thing would be for you to reboot your router regardless of which model you have. Here is the list from ESET:
- “Asus: RT-AC66U, RT-N10, RT-N10E, RT-N10U, RT-N56U, RT-N66U
- D-Link: DES-1210-08P, DIR-300, DIR-300A, DSR-250N, DSR-500N, DSR-1000, DSR-1000N
- Huawei: HG8245
- Linksys: E1200, E2500, E3000, E3200, E4200, RV082, WRVS4400N
- Mikrotik: CCR1009, CCR1016, CCR1036, CCR1072, CRS109, CRS112, CRS125, RB411, RB450, RB750, RB911, RB921, RB941, RB951, RB952, RB960, RB962, RB1100, RB1200, RB2011, RB3011, RB Groove, RB Omnitik, STX5
- Netgear: DG834, DGN1000, DGN2200, DGN3500, FVS318N, MBRN3000, R6400, R7000, R8000, WNR1000, WNR2000, WNR2200, WNR4000, WNDR3700, WNDR4000, WNDR4300, WNDR4300-TN, UTM50
- QNAP: TS251, TS439 Pro, Other QNAP NAS devices running QTS software
- TP-Link: R600VPN, TL-WR741ND, TL-WR841N
- Ubiquiti: NSM2, PBE M5
- Upvel: according to Talos, malware targeting Upvel as a vendor has been discovered, but researchers have not yet determined which devices are targeted.”
Will you reboot your router or reset it?
If you decide you want to “re-set” your router rather than “reboot” it, let us know if you need help.
Information about Geek For Hire, Inc.
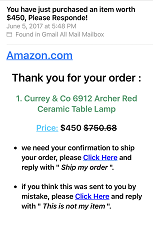
I’ve created a Free Report to protect you from “phishing” scams. Click here to receive it!
Chris Eddy of Geek For Hire, Inc. has been providing computer service to families and small businesses with Mac’s and PCs for the past eighteen years. His company is highly rated by both the BBB and by Angie’s List. You can find more on our website, or give us a call 303-618-0154. Geek For Hire, Inc. provides onsite service (Tier 3) to the Denver / Boulder / Front Range area as well as remote service throughout North America.
We’ve been using Amazon Prime for the past few years. We like the free and fast shipping. With Prime, we have access to online streaming too. Prime is usually $119/year, but you can get a free 30 day trial by clicking on this link: Try Amazon Prime 30-Day Free Trial. As an Amazon Associate, I earn from qualifying purchases.