The winter holidays are coming up fast. We’re stretched thin. We’re planning trips to relatives for holiday meals, planning a holiday party for our work buddies, checking out the kid’s plays and concerts at school, shopping for gifts, and on and on and on.
And the scammers know it. They’re planning Phishing Scams.

Four Ways to Protect Yourself from Phishing Scams:
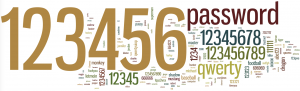
PASSWORDS:
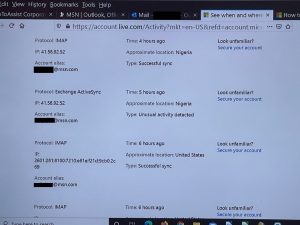
Change your password for ALL your online financial accounts (banks, credit cards, investment, Paypal, etc.), social media accounts, shopping accounts (Amazon, LLBean, REI, etc.), and ANY account where you have saved your credit card info. Do this before Thanksgiving. There have been many data breaches recently, and millions of email/password combinations have been “harvested”. I know! Once you change your password, you must change it on your phone, tablet, computer, and anywhere else you use the app as well. It’s a hassle, but do it. (Here’s a recent blog on creating a secure password.)
PURCHASES:
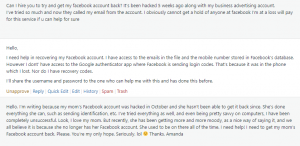
When buying something from an individual online, double-check that they are who they say they are. If they are on Etsy or eBay, check their recent ratings. Do they have a 4.8 star rating overall, but are the recent ratings all ones or twos? Are you buying something from someone you know (or a good friend knows)? Ask them clarifying questions to make sure they haven’t recently been hacked. (Yes, that’s how I got scammed.)
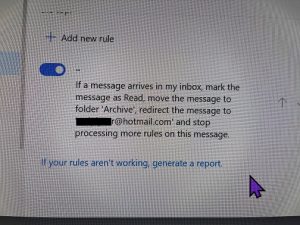
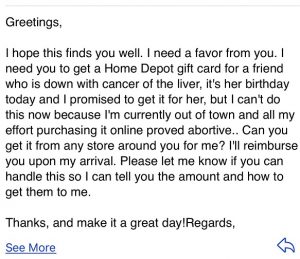
EMAILS:
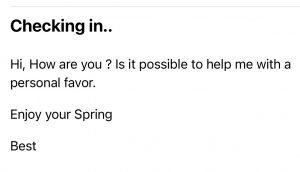
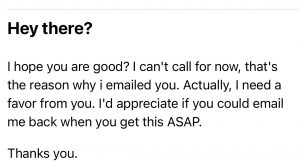
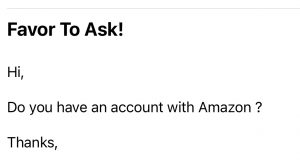
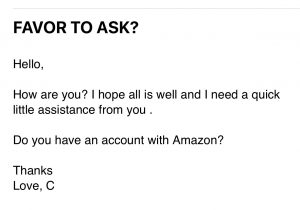
Read your emails very carefully. Scammers know we get a lot of emails this time of year, especially from online shopping accounts. They can guess that we might be ordering from Amazon or Costco and may email us saying there is a “problem” with our order. They want us to click on this handy link they’ve provided. The email has an excellent rendition of the Amazon logo, and they have “spoofed” the URLs to make them look like the link will direct you to Amazon. Don’t fall for it! Go to your account and verify any problems there.
One especially tricky email is from Norton and other anti-virus/security providers. They email that they will process your “subscription renewal” on a future date for big buck$. If you don’t want to renew, just call the number in the email. Then, they ask for permission to access your computer to make sure you don’t have any viruses. If you let them, they’ll have fun. You end up with stolen data and malware on your machine.
TEXTS:
Texts and emails are the most common way to get pulled into phishing scams. By now, we all know that text messages from “USPS” or “FedEx” about delayed deliveries are scams. Read the message carefully. Is it coming from a number you’ve already saved on your phone? Don’t click on that link! Go to the app or website you already have to confirm there is a problem and correct it there.
Conclusion:
Use secure passwords wherever you log in, AND change your passwords frequently. Be incredibly diligent with Social Media and Financial accounts!
“Hey, let’s be careful out there.” (Hill Street Blues)
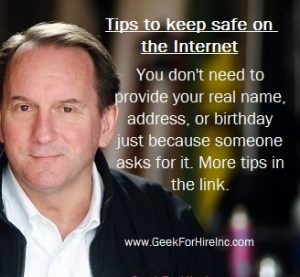
INFORMATION ABOUT GEEK FOR HIRE, INC.
Chris Eddy of Geek For Hire, Inc. has provided computer service to families and small businesses with Mac’s and PCs for the past eighteen years. Angie’s List and the BBB rate Geek For Hire very highly. You can find more on our website, or give us a call. Geek For Hire, Inc. provides onsite service (Tier 3 support) to the Denver / Boulder / Front Range area and remote service throughout North America.
We’ve been using Amazon Prime for the past few years. We like the free and fast shipping. With Prime, we have access to online streaming too. You can get a free 30-day trial by clicking on this link: Try Amazon Prime 30-Day Free Trial. As an Amazon Associate, we earn from qualifying purchases.